Summary
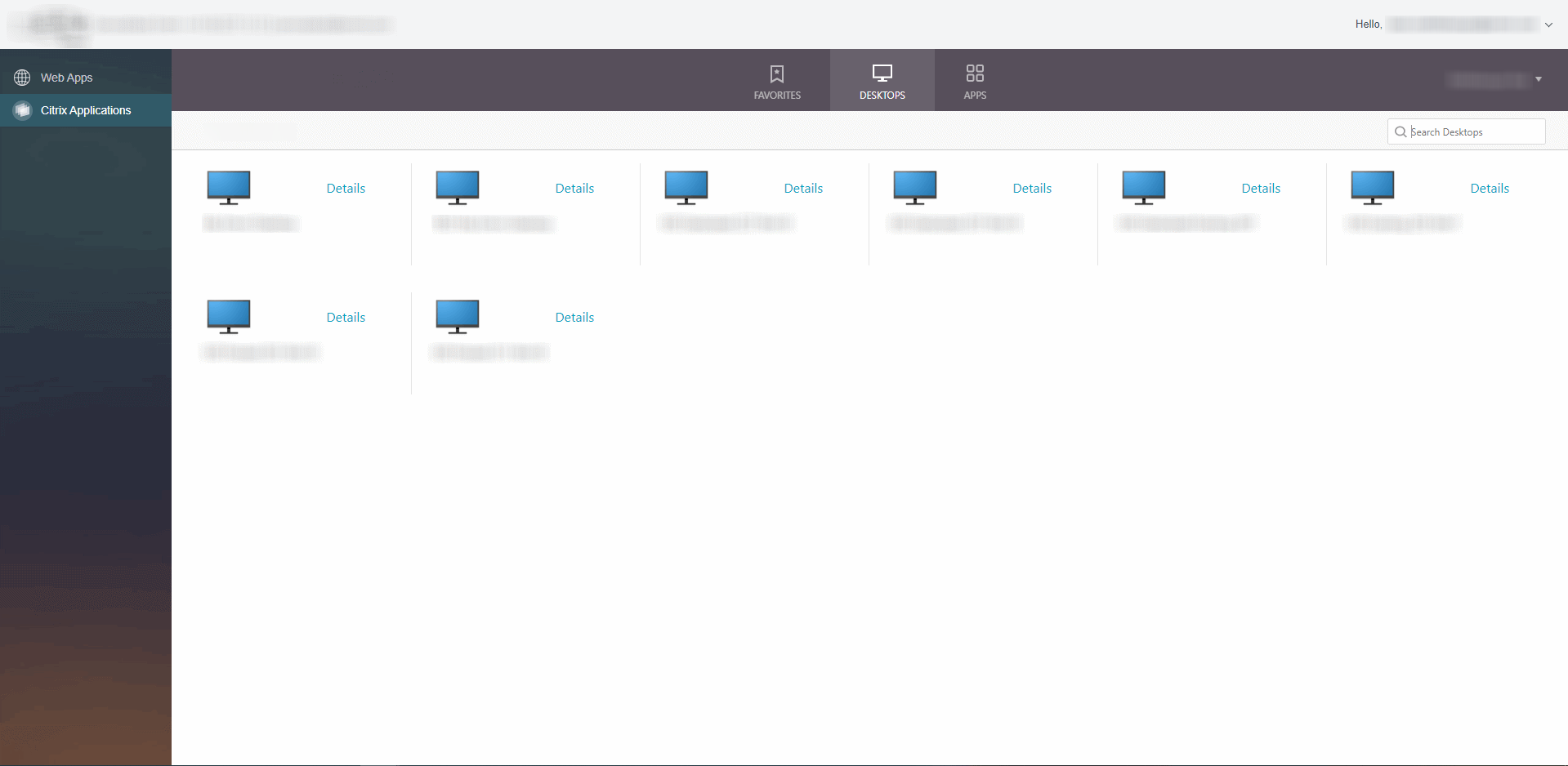
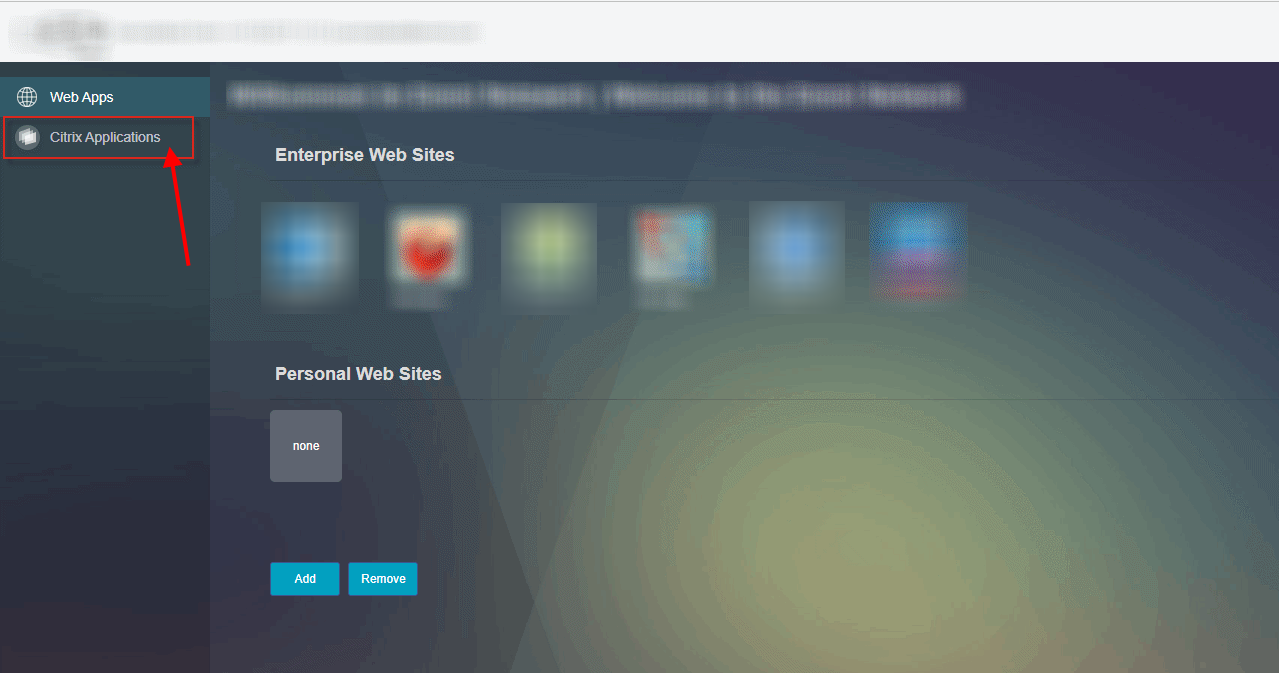
Your company use SSL VPN over Citrix NetScaler for the employees and customers . The employees/customers will get the VPN portal homepage displayed over NetScaler with configured X1 theme.
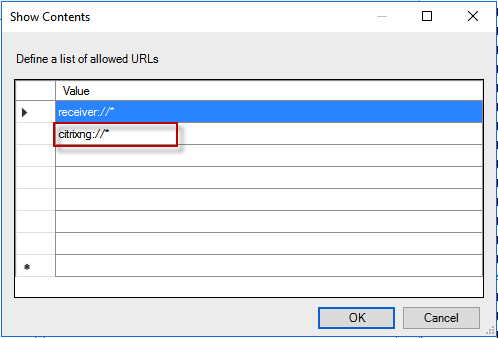
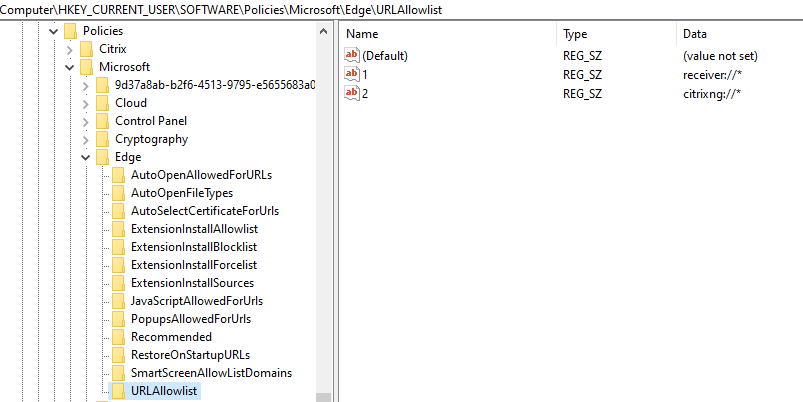
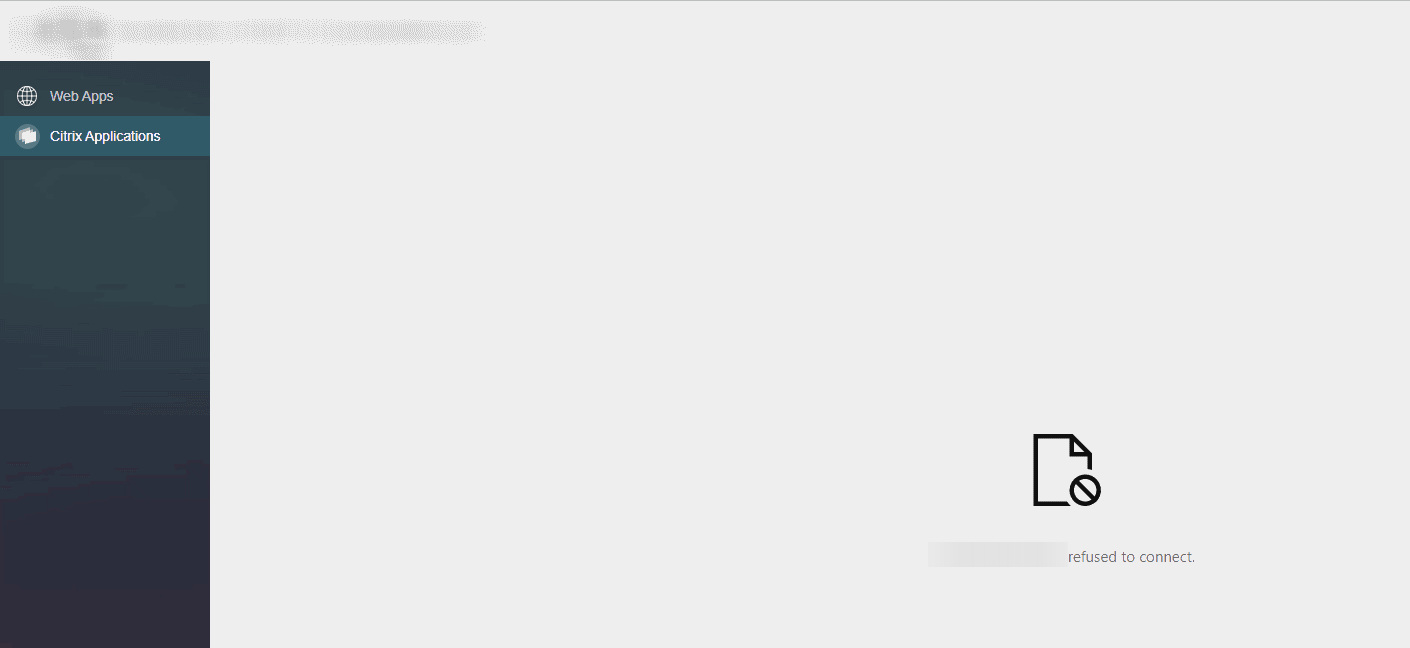
When you click the “Citrix Applications” link on the VPN portal homepage menu, the Citrix Receiver page from the configured session profile should be opened, but the Citrix Receiver page are become refused, when you using a Microsoft Edge Chromium browser.
Description
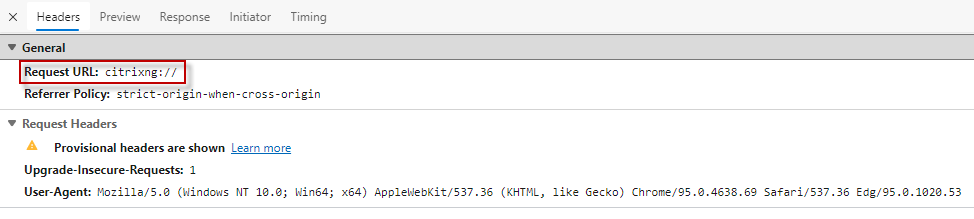
Citrix Storefront X-Frame-Options configuration refuse the HTTP request from the Microsoft Edge Chromium browser, when the request are open through the Citrix NetScaler VPN portal homepage with configured X1 theme.
Maybe you have already configured the X-Frame-Options like the Citrix article CTX202890, the frame-ancestors settings from the article, will not work in combination of Microsoft Egde Chromium browser and the X1 theme from Citrix NetScaler.
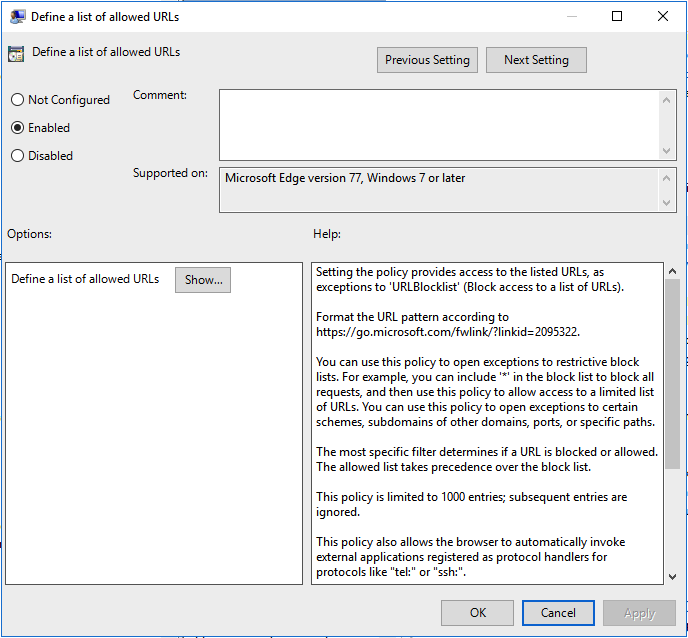
The frame-ancestors settings must be additionally supplemented with the FQDN from the Storefront server or the domain and top-level from your local environment. You can also work with wildcards on the frame-ancestors setting string. From my point of view, this is the easiest and most flexible solution, without reducing the security of the IIS or Microsoft Edge Chromium configuration.
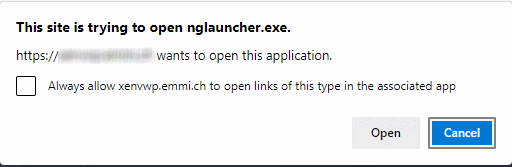
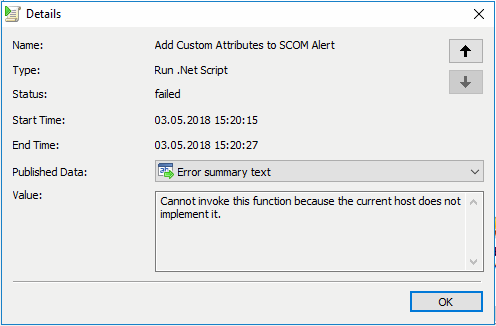
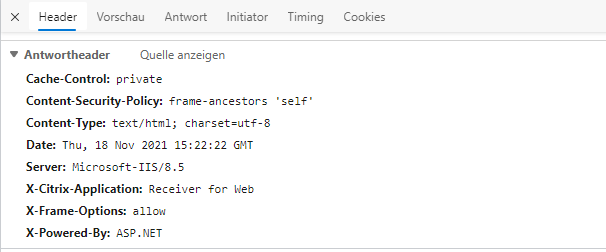
In the developer tools from the Microsoft Egde Chromium you can catch the HTTP response, that displayed the refuse message.
Configuration of the web.config from Citrix Storefront
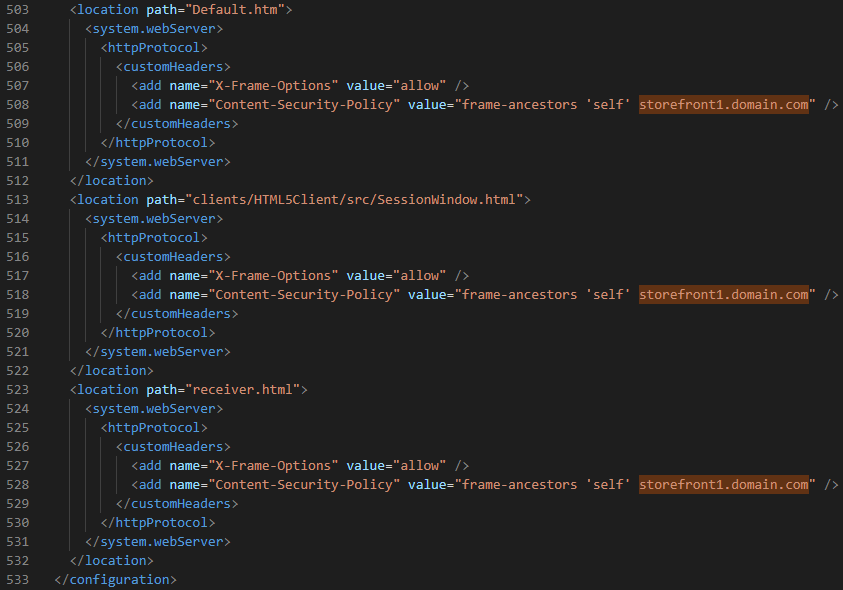
Open the web.config file from your affected Storefront Web Store (drive:/inetpub/wwwroot/citrix/storeweb) and search the statement “X-Frame-Options”. Add following string with your Storefront FQDN or top level domain to the frame-ancestors string, like the following screenshot.
frame-ancestors with Storefront FQDN configuration in the X-Frame-Options
frame-ancestors with wildcard domain and top level configuration in the X-Frame-Options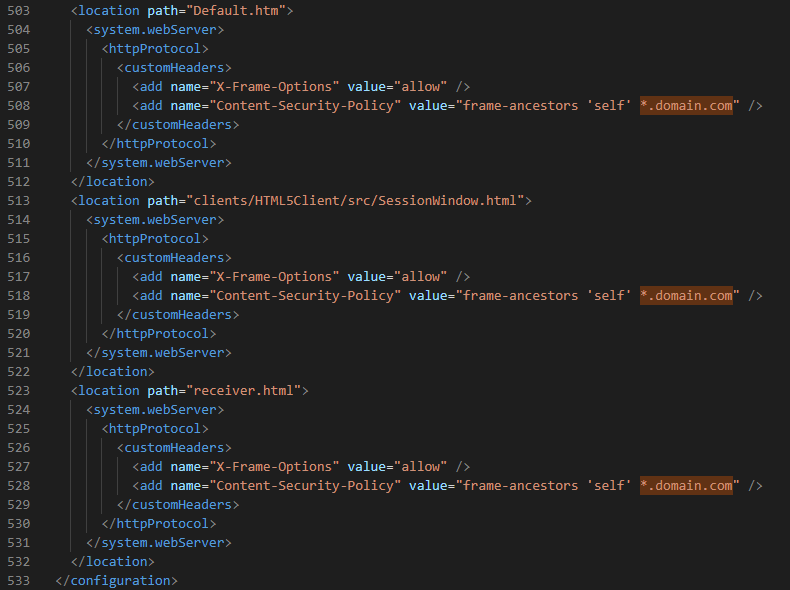
With the configured frame-ancestors in the X-Frame-Options, the Storefront Receiver page will be no longer refused.